Zscaler ThreatLabz on X: "ThreatLabz discovered a #0day #exploit that targeted CVE-2022-37969 on fully patched Windows 10 and Windows 11 systems. This vulnerability was addressed in today's #PatchTuesday. More information can be

Technical Advisory: Dell SupportAssist Local Privilege Escalation (CVE-2021-21518) | NCC Group Research Blog | Making the world safer and more secure
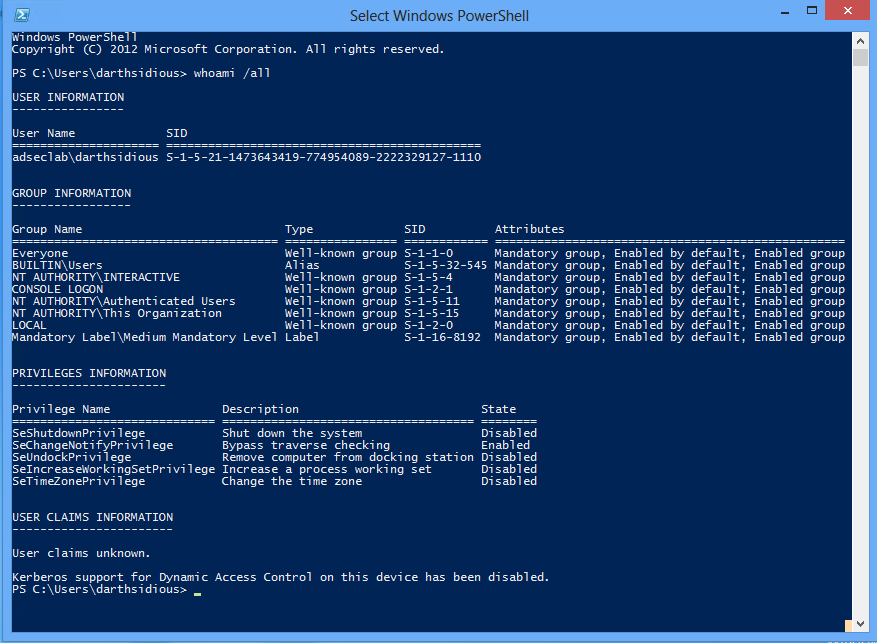
Exploiting MS14-068 Vulnerable Domain Controllers Successfully with the Python Kerberos Exploitation Kit (PyKEK) » Active Directory Security